Cloud computing is the delivery of different services through the Internet. with the help of Top 10 Cloud Computing Projects, we come across These resources of tools and applications like data storage, servers, databases, networking, and software.
It involves the hardware and software components required for the proper implementation of a cloud computing model.
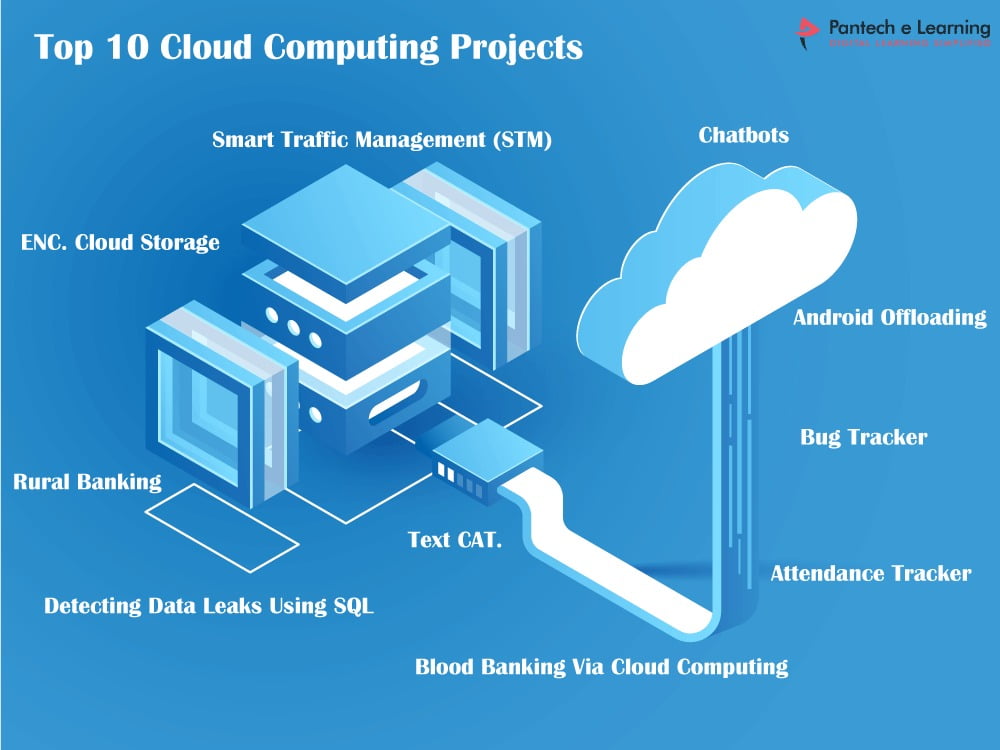
Top 10 Cloud Computing Projects
- Secure File Sharing System using Data Mining
- Secure Data Sharing for Dynamic Groups | Cloud Computing
- Deduplication for Hybrid Cloud Security
- Graphical Password Scheme using Information Security
- Multifarious Data possessor in Network Security
- Malware Detection in Android Application
- Four-factor Authentication
- User-Level Runtime Security Auditing for the Cloud
- Erasure Coding Scheduling Multiblock Updates
Top 10 Cloud Computing Projects involve of
-
Secure File Sharing System using Data Mining
Secure file storing and retrieving mechanism to avoid the limitations in existing systems like file encryption, access rights, and keys management. It provides user access management, encryption, and decryption of files through a trusted third party to make data secure in the system. It is the process of sharing files securely or privately. Most secure file sharing services or software providers enable securing file sharing by restricting access to the file, allowing only authorized personnel to access, view, or download the file.`
-
Secure Data Sharing for Dynamic Groups | Cloud Computing
In cloud computing offers an abstraction of infinite storage space for clients to host data. It can help clients reduce their financial overhead of data management by migrating the local managements system into cloud servers. The cloud computing data center shares performances to the user in efficient way as utilizes the opportunity at right time to the cloud user, quickly availability and efficiency in storage capacity.
-
Deduplication for Hybrid Cloud Security
Data deduplication is one of the data compression techniques for eliminating duplicate copies of repeating data and is widely used in cloud storage to reduce the amount of storage space and save bandwidth. To protect confidential data and the convergent encryption technique has encrypted the data before outsourcing. This technique is used to improve storage utilization.
-
Graphical Password Scheme using Information Security
Graphical Systems are a potential replacement or supplement for conventional authentication systems. It offers greater resistance to capture attacks against graphical authentication include intercepted communication and spyware. A graphical-based password is one promising alternatives of textual passwords. The new hybrid graphical password-based system which is a combination of recognition and based techniques that offers many advantages over the existing systems are more convenient for the user.
-
Multifarious Data possessor in Network Security
Information hiding mechanisms can be applied to prevent the secret data from the intruder or malicious modification. Network Security is a procedure of obtaining information secure with more integrity and confidentiality. It is the process of safeguarding important information from corruption and loss. The importance of data protection increases as the amount of data created and stored continues to grow at unprecedented rates.
-
Malware Detection in Android Application
Security is an important aspect of human existence in a world, with inadequate security as it becomes the safety of the users. Malware detection techniques identify gaps and provide the basis for improving effective measure for unknown android malware. The results showed that it is a more promising approach with higher detection accuracy. The realization of static and dynamic malware analysis techniques and principles that can be automated and mapped to software system tools in order to simplify analyses.
-
Four-factor Authentication
Four factor systems are used in a business and government agencies require high security. The high levels of multifactor authentication make it increase that an attacker can steal all elements involved. The process of authentication for a user is consider to be most vital and important in the field of computing systems, most of the conventional authentication process depends on one or all the three factors such as a password or a fingerprint and sometimes even through SMS or Voice.
-
User-Level Runtime Security Auditing for the Cloud
A privacy-preserving mechanism that supports public auditing on data stored in the cloud. It is identity on each block of shared data is kept private from the public to verifies data integrity without retrieving the file. It performs multiple auditing tasks simultaneously instead of verifying one by one. The propose a runtime security auditing framework for the cloud with special focus on the user-level including authentication mechanisms and implement to evaluate the framework based on deployed cloud management system.
-
Erasure Coding Scheduling Multiblock Updates
The theoretical analysis verifies that can effectively reduce the overhead when multiple blocks are update. It implements a prototype storage system to deploy with the different erasure codes. The experimental results can reduce and improve storage system of update approaches.
