Description
Secure Data Sharing for Dynamic Groups | Cloud Computing
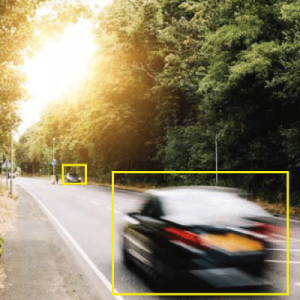
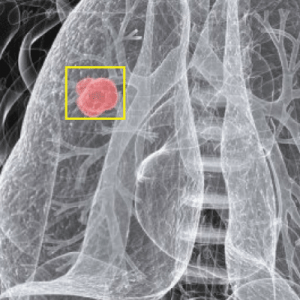
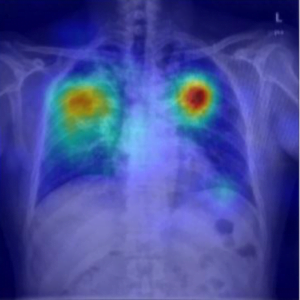
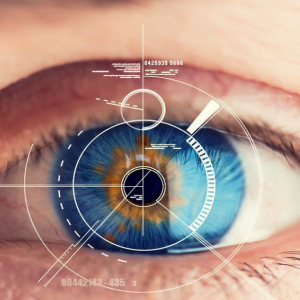
Cyber Attacks, with the characteristics of intrinsic data sharing and low maintenance, provides a better utilization of resources. In cloud computing, cloud service providers offer an abstraction of in?nite storage space for clients to host data. It can help clients reduce theirs? the financial overhead of data managements by migrating the local managements system into cloud servers. Secure Data Sharing for Dynamic Groups | Cloud Computing
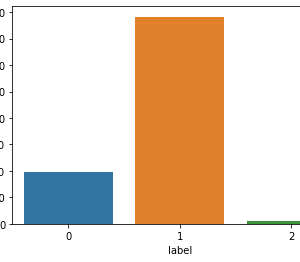
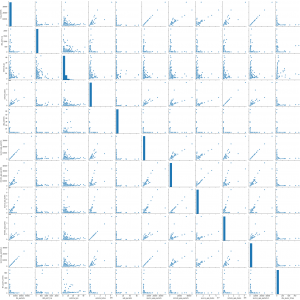
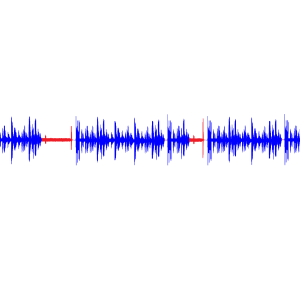
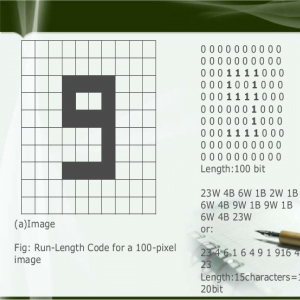
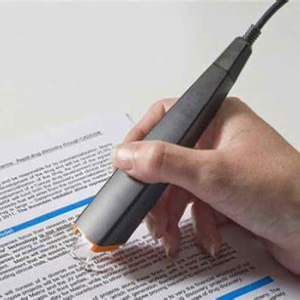
The characteristics of intrinsic information sharing and low maintenance, provides a more robust utilization of resources. In cloud computing, cloud service suppliers provide associate degree abstraction of infinite cupboard space for shoppers to host information. It will facilitate shoppers to scale back their money overhead of information management by migrating the native management system into cloud servers. However, security issues become the most constraint as we have a tendency to currently source the storage of information that is probably sensitive, to cloud suppliers. To preserve information privacy, a typical approach is to inscribe information files before the shoppers transfer the encrypted information into the cloud. Sadly, it’s tough to style a secure and economical information sharing theme, particularly for dynamic teams within the cloud. Presented a crypto graphical storage system that allows secure information sharing on devious servers supported the techniques that dividing files into file groups and encrypting every file group with a file-block key. However, the file-block keys have to be compelled to be updated and distributed for a user revocation, here for; the system had a significant key distribution overhead. Alternative schemes for information sharing on un-trusted servers are planned. However, the complexities of user participation and revocation in these schemes square measure linearly increasing with the quantity of information house owners and also the revoked users. Secure Data Sharing for Dynamic Groups | Cloud Computing
EXISTING SYSTEM:
Several security schemes for data sharing on un-trusted servers have been proposed. In these approaches, data owners store the encrypted data files in un-trusted storage and distribute the corresponding decryption keys only to authorized users. Thus, unauthorized users as well as storage servers cannot learn the content of the data files because they have no knowledge of the decryption keys However, the complexities of user participation and revocation in these schemes are linearly increasing with the number of data owners and the number of revoked users, respectively. By setting a group with a single attribute, Lu et al. proposed a secure provenance scheme based on the cipher text-policy attribute-based encryption technique, which allows any member in a group to share data with others. However, the issue of user revocation is not addressed in their scheme. They presented a scalable and fine-grained data access control scheme in cloud computing based on the key policy attribute-based encryption (KP-ABE) technique. Unfortunately, the single owner manner hinders the adoption of their scheme into the case where any user is granted to store and share data. Secure Data Sharing for Dynamic Groups | Cloud Computing
DISADVANTAGES:
- The file-block keys need to be updated and distributed for a user revocation; therefore, the system had a heavy key distribution overhead.
- The complexities of user participation and revocation in these schemes are linearly increasing with the number of data owners and the revoked users.
- The single-owner manner may hinder the implementation of applications, where any member in the group can use the cloud service to store and share data files with others. Secure Data Sharing for Dynamic Groups | Cloud Computing
PROPOSED SYSTEM:
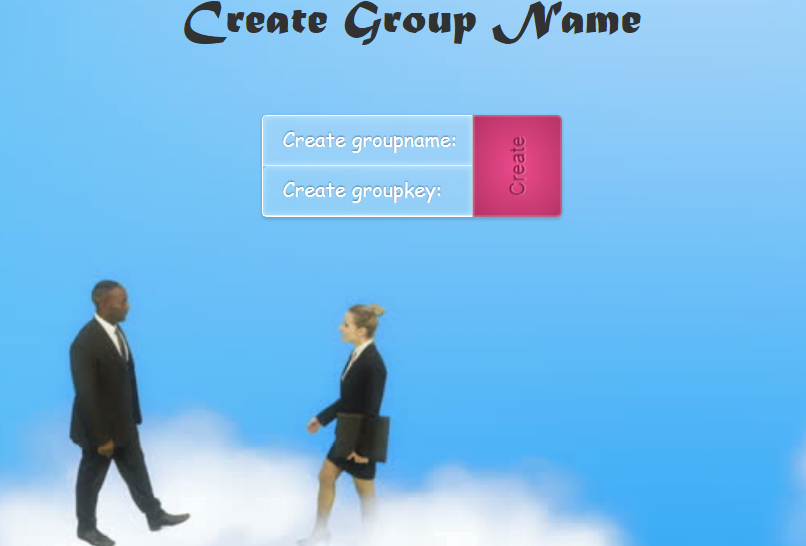
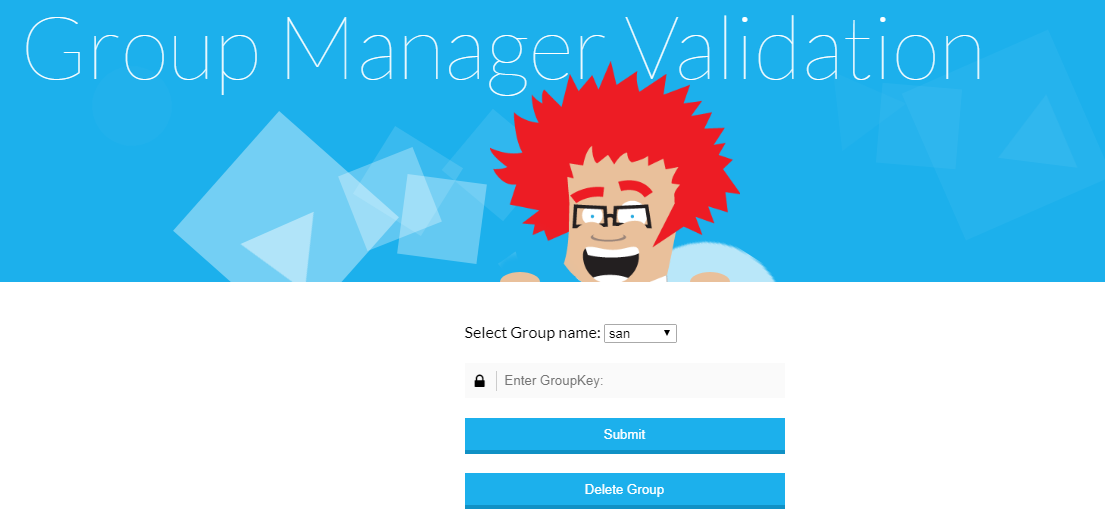
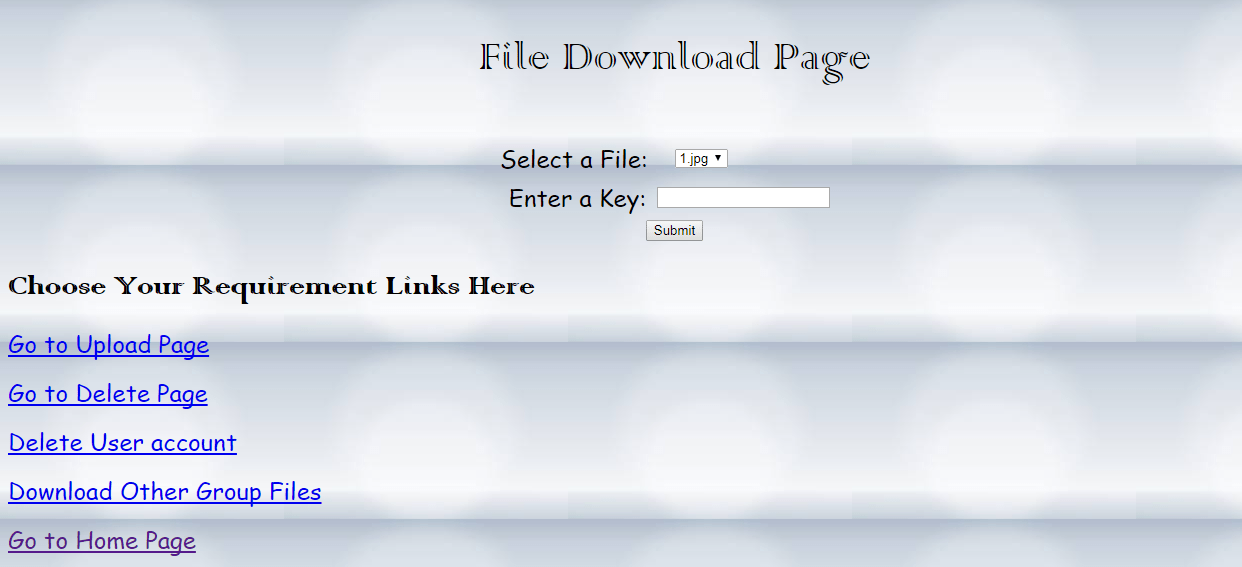
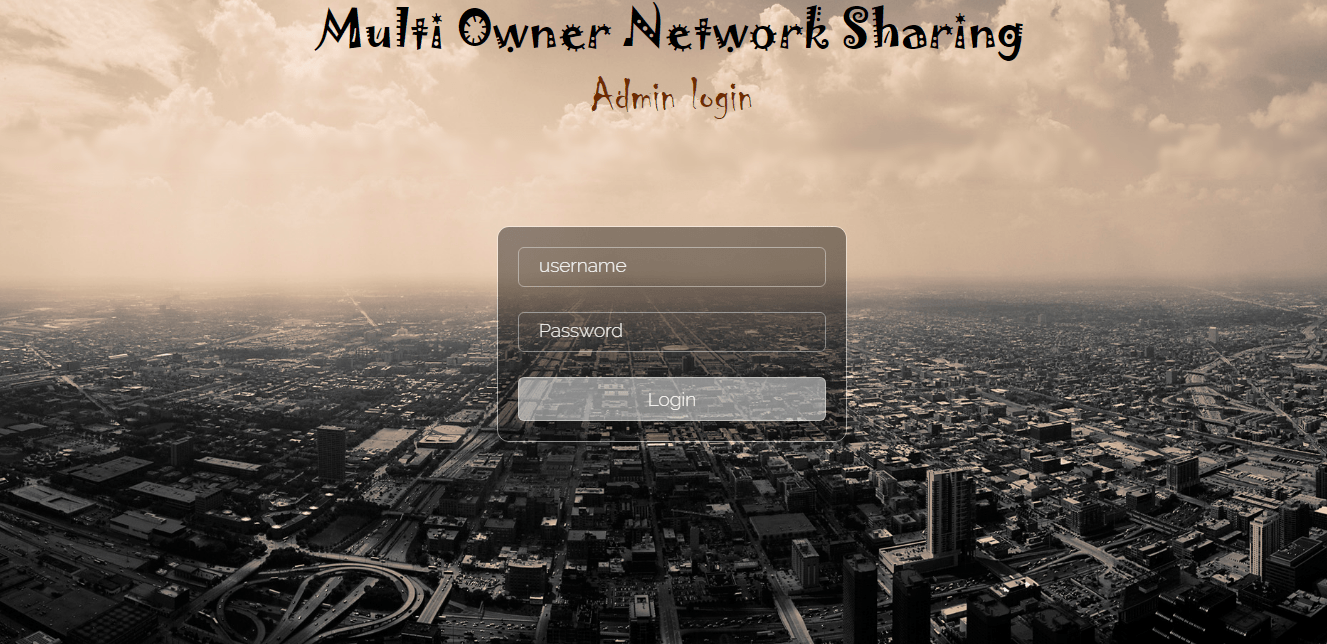
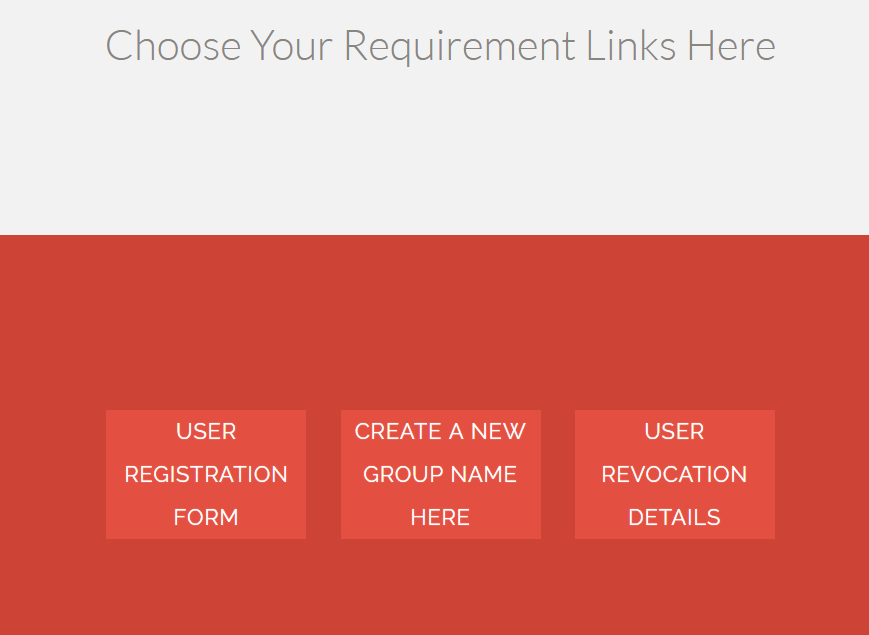
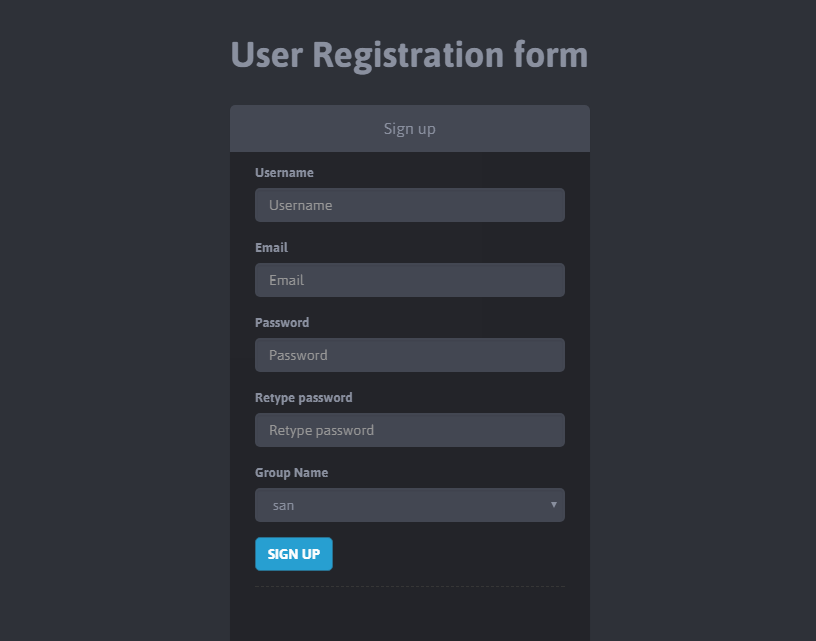
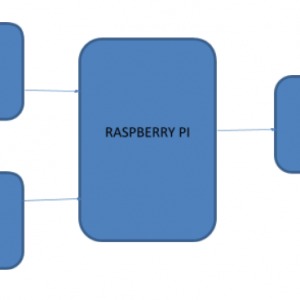
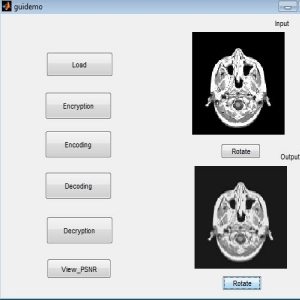
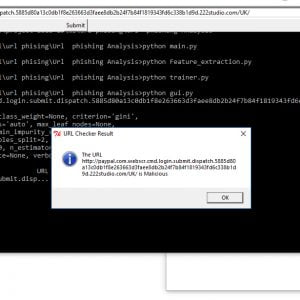
Anti-collusion information sharing scheme for dynamic companies within the cloud, the customers can securely btain their private keys from team manager certificates Authorities and secure communication channels. Also, our scheme is equipped to help dynamic corporations efficiently, when a brand new user joins within the workforce or a consumer is revoked from the group, the confidential keys of the opposite customers do not have to be recomputed and updated. Moreover, our scheme can reap at ease user revocation; the revoked customers cannot be equipped to get the usual data documents as soon as they are revoked even though they conspire with the un-trusted cloud. Secure Data Sharing for Dynamic Groups | Cloud Computing
ADVANTAGES:
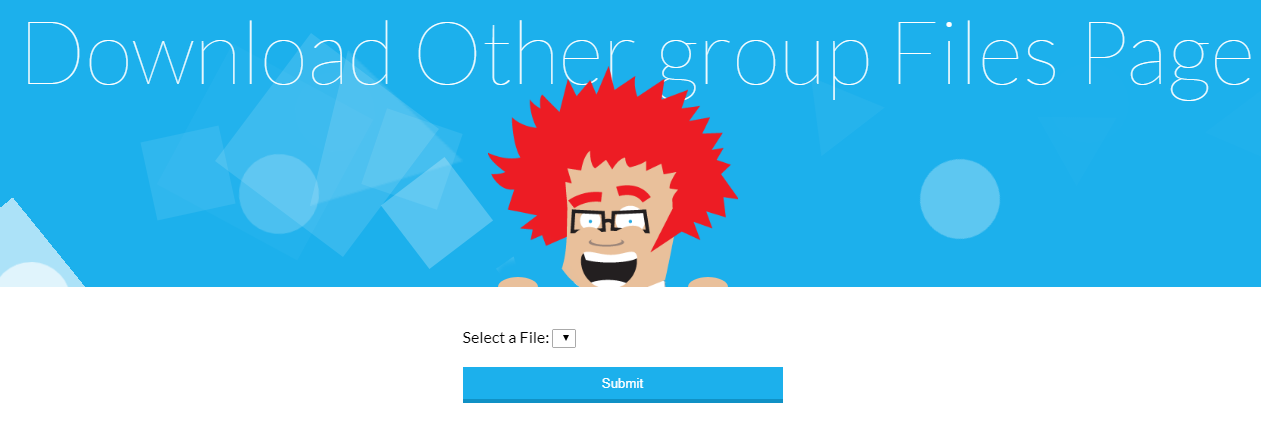
- We propose a secure Anti-collusion information sharing scheme for dynamic companies data sharing scheme. It implies that any user in the group can securely share data with others by the un-trusted cloud.
- We provide secure and privacy-preserving access control to users, which guarantees any member in a group to anonymously utilize the cloud resource. Secure Data Sharing for Dynamic Groups | Cloud Computing
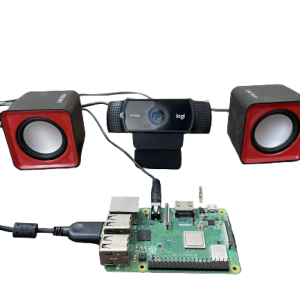
HARDWARE AND SOFTWARE SPECIFICATION:
Software Requirement:
- OS -?????????? Windows 7,10
- MySql Server
- NetBeans IDE
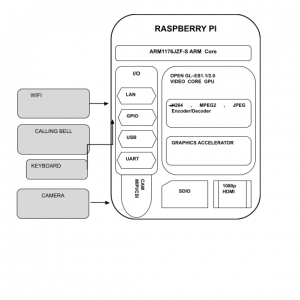
Hardware Requirement:
- 2 GB RAM
- 80 GB Hard Disk
- Above 2GHz Processor
- Data Card
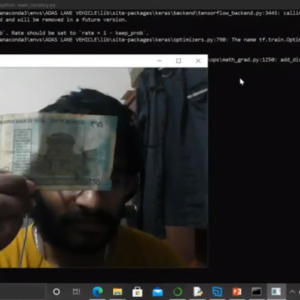
TECHNOLOGY USED:
Programming Language : Java
Apllication??????????? ??????????? : Servlet,MVC
Web Server????????????????????? : Glashfish Server
Front end Language?????? 😕 JSP,Java Script,CSS
Back End ??????????????????????????????????? 😕 MySql Server,Sql Yog


































































































































































































































































































































































































































































































































































































































































Customer Reviews
There are no reviews yet.