Description
Channel Allocation Scheme Based On Greedy Algorithm In Cognitive Vehicular Network
ABSTRACT
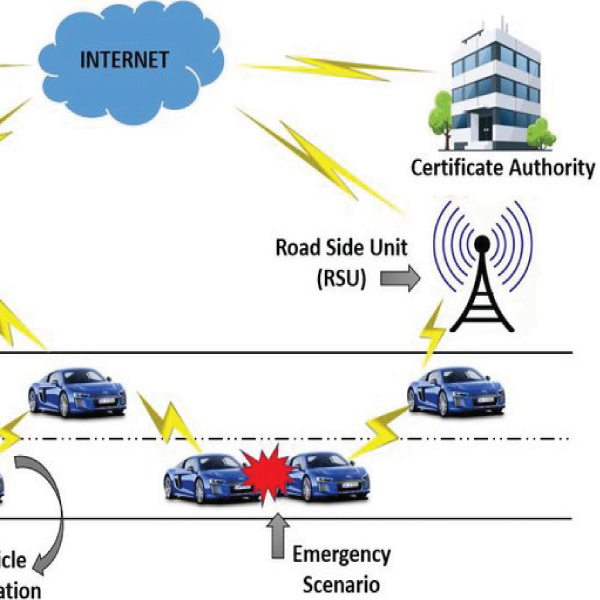
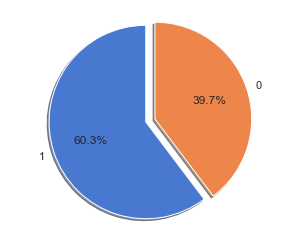
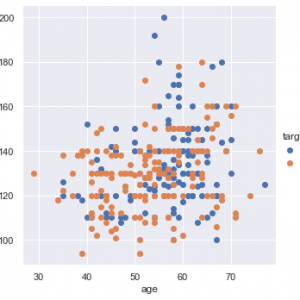
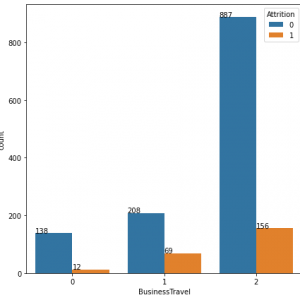
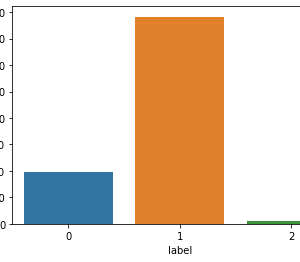
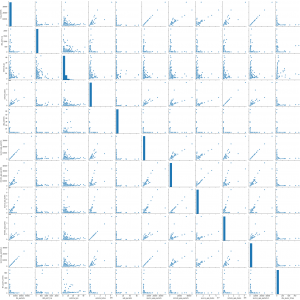
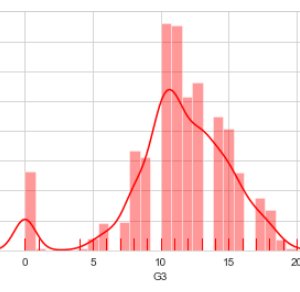
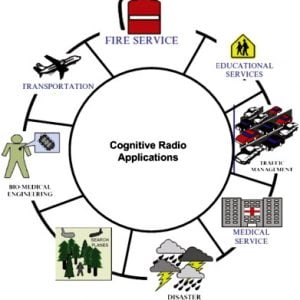
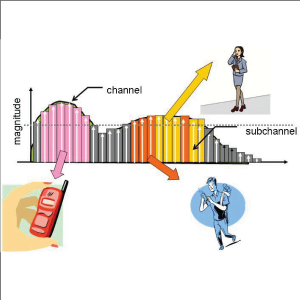
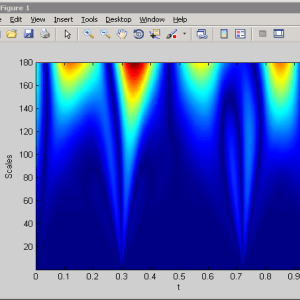
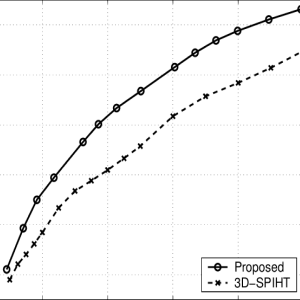
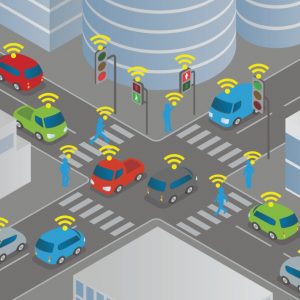
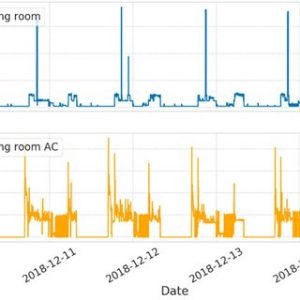
The cognitive radio (CR) concept is turning out as a prominent approach used in the wireless communication network for increasing spectrum efficiency by opportunistically and mutually sharing the spectrum of contemporary networks. CR can bear high traffic loads during emergencies and major disasters by overcoming the limitations like lack of network capacity. The fundamental issues pertaining to the implementation of CR network (CRN) are the presence of co-channel interference and adjacent channel interference among CR users; and most importantly interference to primary users. Effective interference mitigation and management in CRN will make it more robust in easing the additional stress because of very high traffic loads during intense emergency and disaster scenarios. In this study, an approach has been taken to minimize interference among secondary nodes by employing an interference index as an interference minimization key which in turn maximizes the system capacity. To validate the results, the authors thoroughly used an existing distributed greedy algorithm, which, on the introduction of the interference index, furnished a gain of 60% in the CR network capacity. Further, a trade-off analysis between the interference index and channel leakage ratio is presented with an interference bound of 10dB, which may form the basis of interference management in CRN. Channel Allocation Scheme Based On Greedy Algorithm In Cognitive Vehicular Network
EXISTING METHOD
- Energy-efficient RB Allocation Algorithm
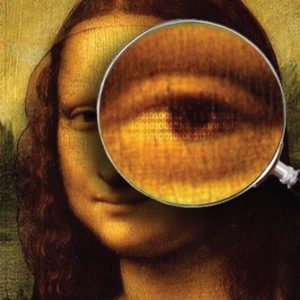
- In the network layer, advanced cryptographic schemes are availed for data security to avoid eavesdropper intervention.
DRAWBACKS
- Low throughput rate with the UE increase in the change also.
- Secret cryptography and key management should be made with much more advancement enabled this make much complicated of the system
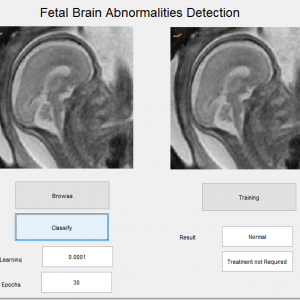
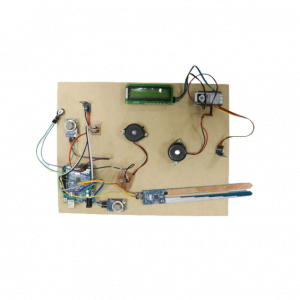
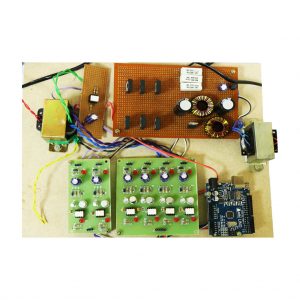
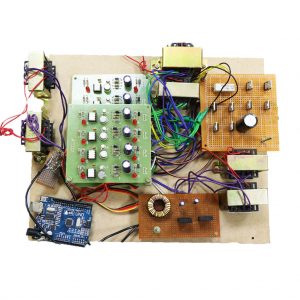
PROPOSED METHOD
- LTE network with decode and forward relaying strategy with high throughput analysis over the existing system and real-time system analysis.
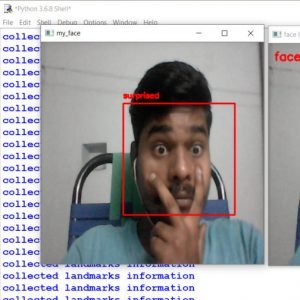
- Eavesdropper analysis.
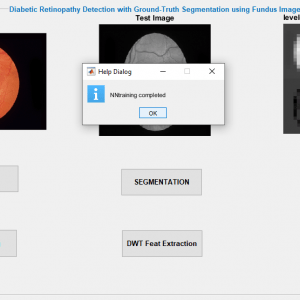
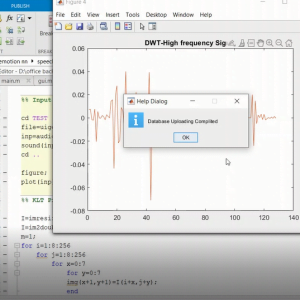
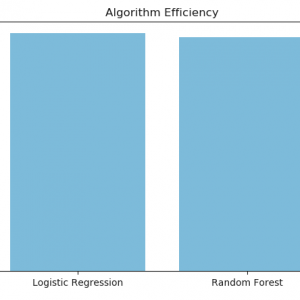
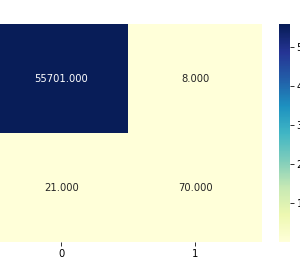
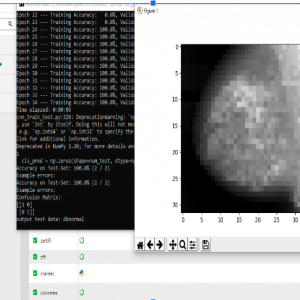
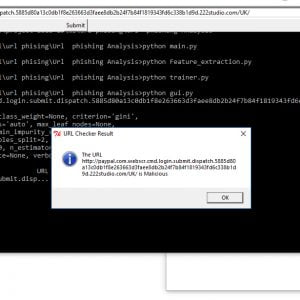
- Distributed Greedy Algorithm
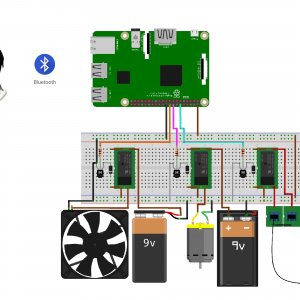
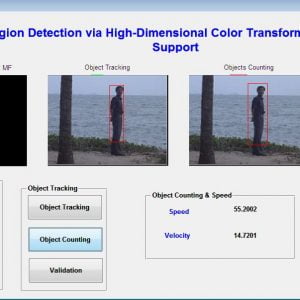
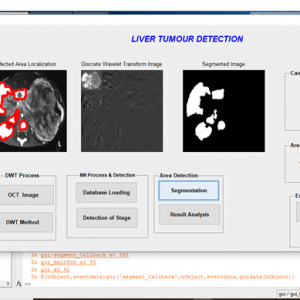
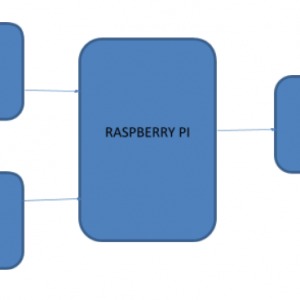
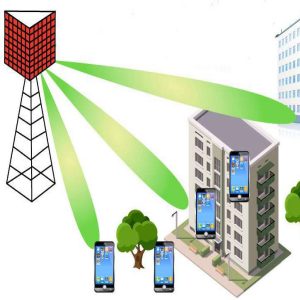
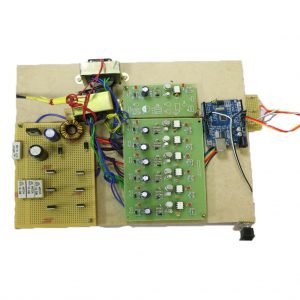
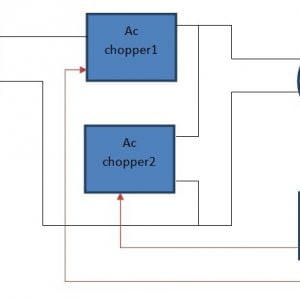
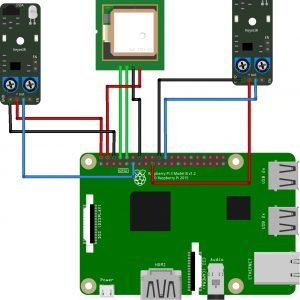
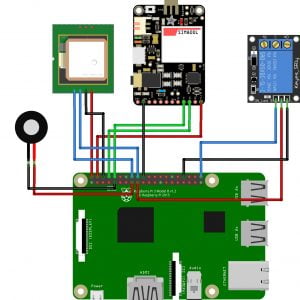
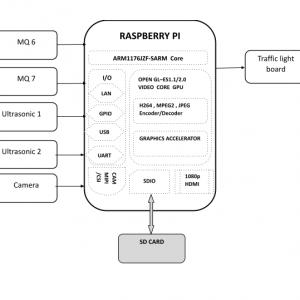
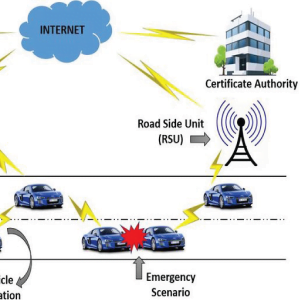
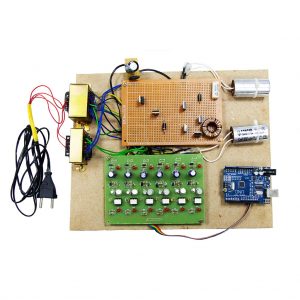
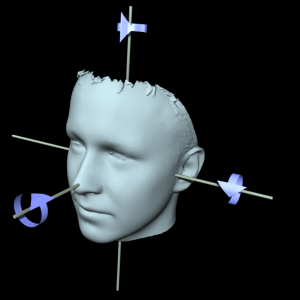
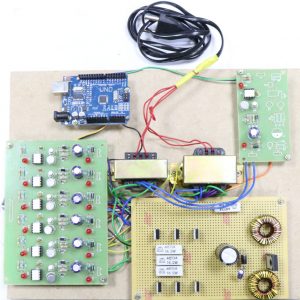
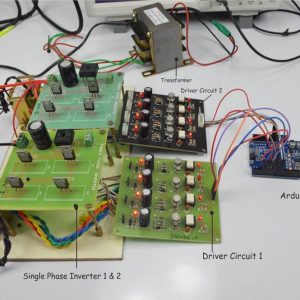
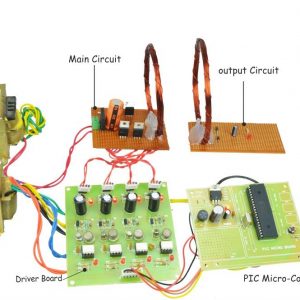
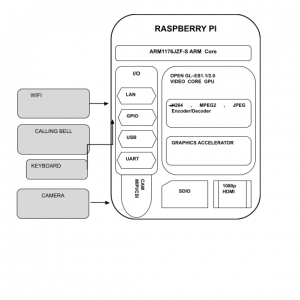
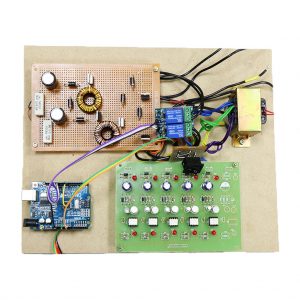
BLOCK DIAGRAM
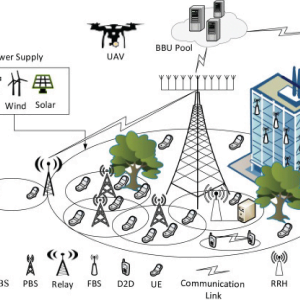
- PBS Primary base station PU: primary user
- MSU Macrocell secondary user
- FBS Femtocell base station
- FSU?Femtocell secondary user
ADVANTAGES:
- The action occurs much more in the physical layer hence the data is transferring toward the eavesdropper can be efficiently avoided.
- The relay selection plays a vital role here and the schemes are fewer.
APPLICATIONS:
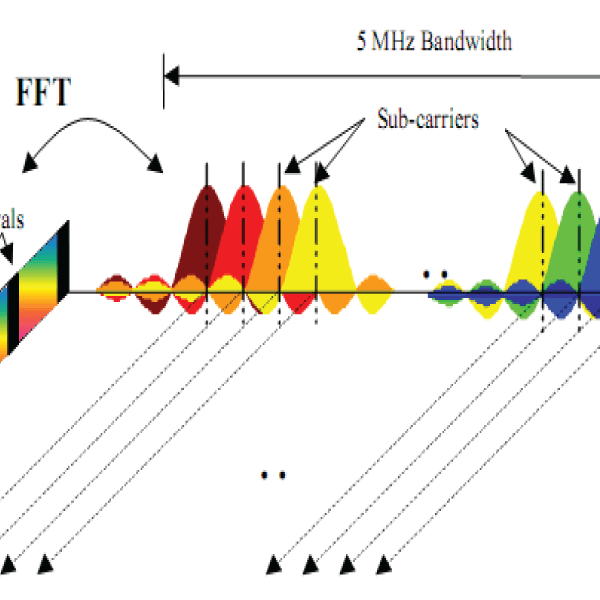
- Multi-carrier signal transmission for video conferencing and high data rate WIMAX system communication
- Normal multipath fading system analysis networks
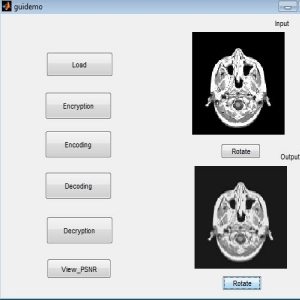
SOFTWARE REQUIREMENT
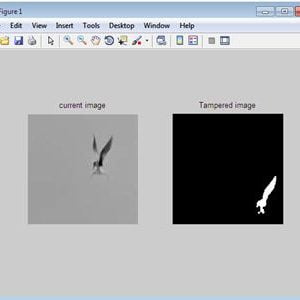
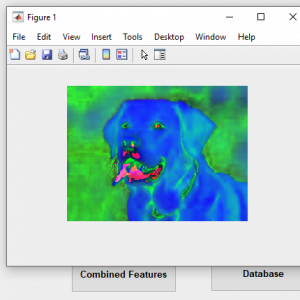
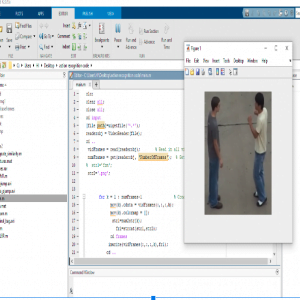
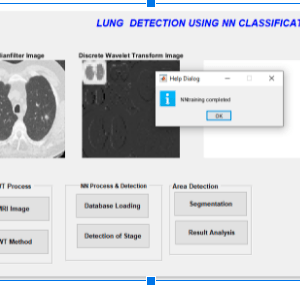
- MATLAB 2018 or above versions
REFERENCES
[1] K. I. Pedersen, F. Frederiksen, C. Rosa, et al.. ?Carrier aggregation for LTE-advanced: functionality and performance aspects.? IEEE Communications Magazine, vol. 49, pp. 89-95, Jun. 2011.
[2] Qualcomm. ?LTE in unlicensed spectrum: Harmonious coexistence with Wi-Fi.? White Paper, Jun. 2014.
[3] R. Zhang, M. Wang, L. X. Cai, Z. Zheng, X. Shen, and L. L. Xie. ?LTEunlicensed: the future of spectrum aggregation for cellular networks.? IEEE Wireless Communications, vol. 22, pp. 150-159, Jun. 2015.
[4] F. Abinader, E. Almeida, F. Chaves, et al.. ?Enabling the coexistence of LTE and Wi-Fi in unlicensed bands.? IEEE Communications Magazine, vol. 52, pp. 54-61, Nov. 2014.
[5] A. M. Cavalcante et al.. ?Performance Evaluation of LTE and WiFi Coexistence in Unlicensed Bands.? in 2013 IEEE 77th Vehicular Technology Conference (VTC Spring), Dresden, pp. 1-6, 2013.
[6] M. I. Rahman, A. Behravan, H. Koorapaty, J. Sachs, and K. Balachandran. ?License-exempt LTE systems for secondary spectrum usage: scenarios and ?rst assessment.? in IEEE Symposium on New Frontiers in Dynamic Spectrum Access Networks (DySPAN), pp. 349-358, 2011.
[7] A. Babaei, J. Andreoli-Fang and B. Hamzeh. ?On the impact of LTE-U on Wi-Fi performance.? in 2014 IEEE 25th Annual International Symposium on Personal, Indoor, and Mobile Radio Communication (PIMRC), Washington DC, pp. 1621-1625, 2014.
[8] S. Y. Lien, J. Lee and Y. C. Liang. ?Random Access or Scheduling: Optimum LTE Licensed-Assisted Access to Unlicensed Spectrum.? IEEE Communications Letters, vol. 20, pp. 590-593, Mar. 2016.
[9] H. Cui, V. C. M. Leung, S. Li and X. Wang. ?LTE in the Unlicensed Band: Overview, Challenges, and Opportunities.? IEEE Wireless Communications, vol. 24, pp. 99-105, 2017.
[10] A. Mukherjee et al.. ?Licensed-Assisted Access LTE: coexistence with IEEE 802.11 and the evolution toward 5G.? IEEE Communications Magazine, vol. 54, pp. 50-57, Jun. 2016.






























































































































































































































































































































































































































































































































































































































































Customer Reviews
There are no reviews yet.